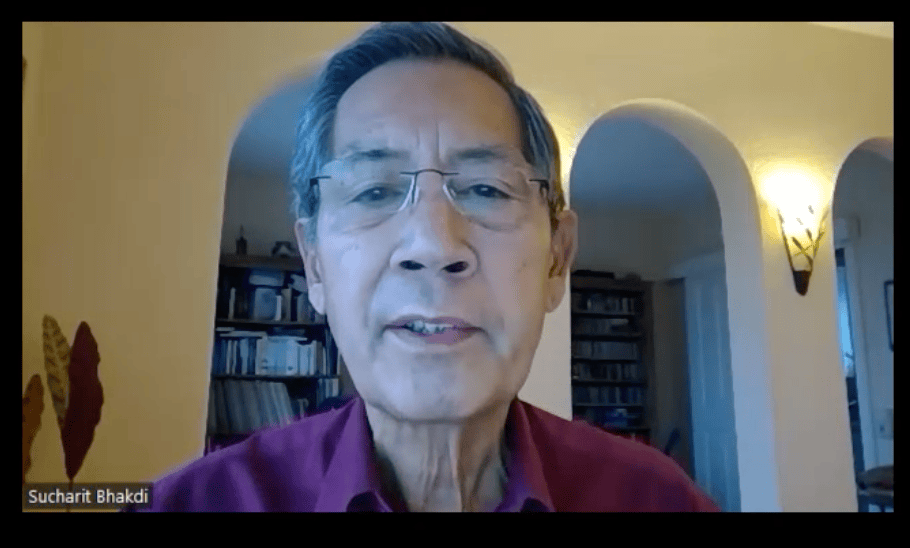
Watch Here in multiple languages: https://www.mwgfd.org/mydatamychoice-bhakdi-en/
Disclaimer: We at Prepare for Change (PFC) bring you information that is not offered by the mainstream news, and therefore may seem controversial. The opinions, views, statements, and/or information we present are not necessarily promoted, endorsed, espoused, or agreed to by Prepare for Change, its leadership Council, members, those who work with PFC, or those who read its content. However, they are hopefully provocative. Please use discernment! Use logical thinking, your own intuition and your own connection with Source, Spirit and Natural Laws to help you determine what is true and what is not. By sharing information and seeding dialogue, it is our goal to raise consciousness and awareness of higher truths to free us from enslavement of the matrix in this material realm.
 EN
EN FR
FR


















Very important as to this post.
"As one may have passed the old addy of "the 666" the Beast is it. "
Every single device we all operate electronically is rigged to pass your every mouse click the every index capture of all files contained. The add too remove from installed de-installed. call from too sms to mms too/from etc etc etc. Who's watching you watch your smart TV. via the pixel camera in the middle of your screen. monitor etc. It is all collected in similar fashion.
The Very Operating system you click by and smile with. All is recorded packet processed Encrypted to compressed meta data. Everytime you shut down and reboot the next day. Before your desktop is loaded all that previous days packet of data is sent to Collection Servers only to be used against you. Un-knowingly and without any consent. Even Linux too as once said more secure is now fully infiltrated to also capturing this user meta data. {there are a few still to whom what are not as infiltrated -there is a butt- }.
Most is extracted no matter how hardened you think your firewall proxy'd vpn services think to provide. Everything is recorded and used in this way. Test some and cursor down to key and mouse position – "deviceinfo.me" in your browser and observe the detail. Everything is funnel opened into and out of every browser connected to the internet. {this is just one site of few}.
Anything connected to the internet is "Un-Safe" This site does show of the last character typed. What is of the many full keys tapped daily, ie: passwds one types is also collected. Cached and placed in various parts onto storage that can be retrieved by this mastery of disguise. An old addy says.
Be Afraid be Really afraid. Well this is the truth about internet of all things. AI too is also collecting this live. My even thought to now with some super Computers is may also be secretly grabbing data houses all encrypted DB all to service their own Intrusion access to the most deepest levels. So think hard and long on this one. This is where it has reached. And you say.. Poop on that. Right on.. Carry on then. lack of knowledge is no defense.
oh PS: With one leader of such as to now you only have thin client access to your own – work type Product and online cloud/crowd feature. No matter what you type there is extracted mistakes and all backspace and all direct on these types of services captured/collected/compressed on those platforms direct.
So its only about learning to what these unknowns are doing with your personal information points of detail. Pegasses and other intrusion devices are all set for such a stage operation.
Some might call it the battle field of todays data transcription to transfer bits and bytes by. Back to the Carrier Pigeon might be a new choice to reconsider.
Or the athletic "Runner/Couriers". Jerome Corsi had a public voice once mentioned all this on his last drag away from podium share. all similar reveal. Good Post.!